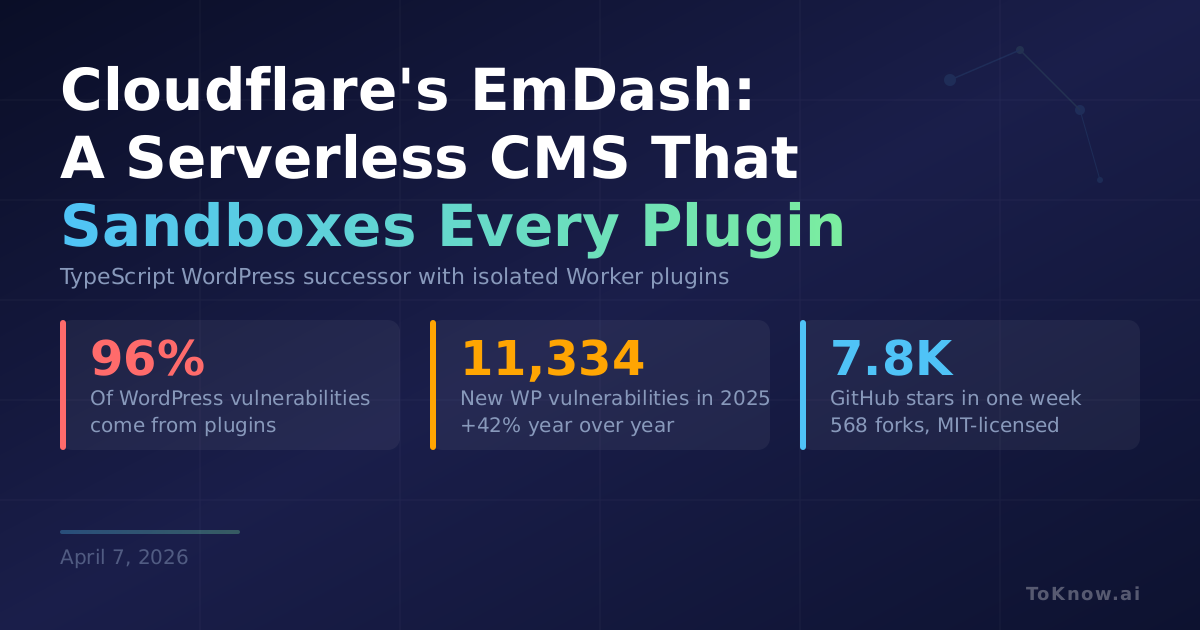
Cloudflare released the beta of EmDash, a TypeScript CMS built on Astro that it calls “the spiritual successor to WordPress.” The headline feature is plugin sandboxing. WordPress plugins share the CMS’s PHP process with full database and filesystem access. 96% of WordPress vulnerabilities come from plugins, and Patchstack counted 11,334 new ones in 2025, up 42% year over year. EmDash runs each plugin in its own Dynamic Worker isolate with a capability manifest: a plugin requesting read:content and email:send can do exactly those two things, nothing else. The project hit 7,800 stars in a week. It’s MIT-licensed with WordPress import tooling, passkey auth, and a built-in MCP server.
Patchstack found the median time from disclosure to mass exploitation was 5 hours in 2025, and 46% of plugin vulnerabilities never got patched. EmDash turns plugin trust into a readable manifest instead of a code audit. Sandboxed plugins require Cloudflare’s $5/month paid tier. Self-hosted Node.js installs lose the sandbox.
WordPress won on its ecosystem of 60,000+ plugins, not code quality, and EmDash starts at zero. The 694-point Hacker News debate was skeptical. But the security architecture is sound: declare what a plugin can do, enforce it at the runtime level, stop trusting code you haven’t read.
Sources:
- Cloudflare Blog: Introducing EmDash
- EmDash GitHub Repository (7.8K stars)
- Patchstack: State of WordPress Security in 2025
- Patchstack: State of WordPress Security in 2026
- Hacker News Discussion (694 points)
Disclaimer: For information only. Accuracy or completeness not guaranteed. Illegal use prohibited. Not professional advice or solicitation. Read more: /terms-of-service
Reuse
Citation
@misc{kabui2026,
author = {{Kabui, Charles}},
title = {Cloudflare’s {EmDash:} {A} {Serverless} {TypeScript} {CMS}
{That} {Sandboxes} {Every} {Plugin}},
date = {2026-04-07},
url = {https://toknow.ai/posts/cloudflare-emdash-cms-wordpress-successor-sandboxed-plugins/},
langid = {en-GB}
}